Ransomware Attack Today: Understanding Modern Threats
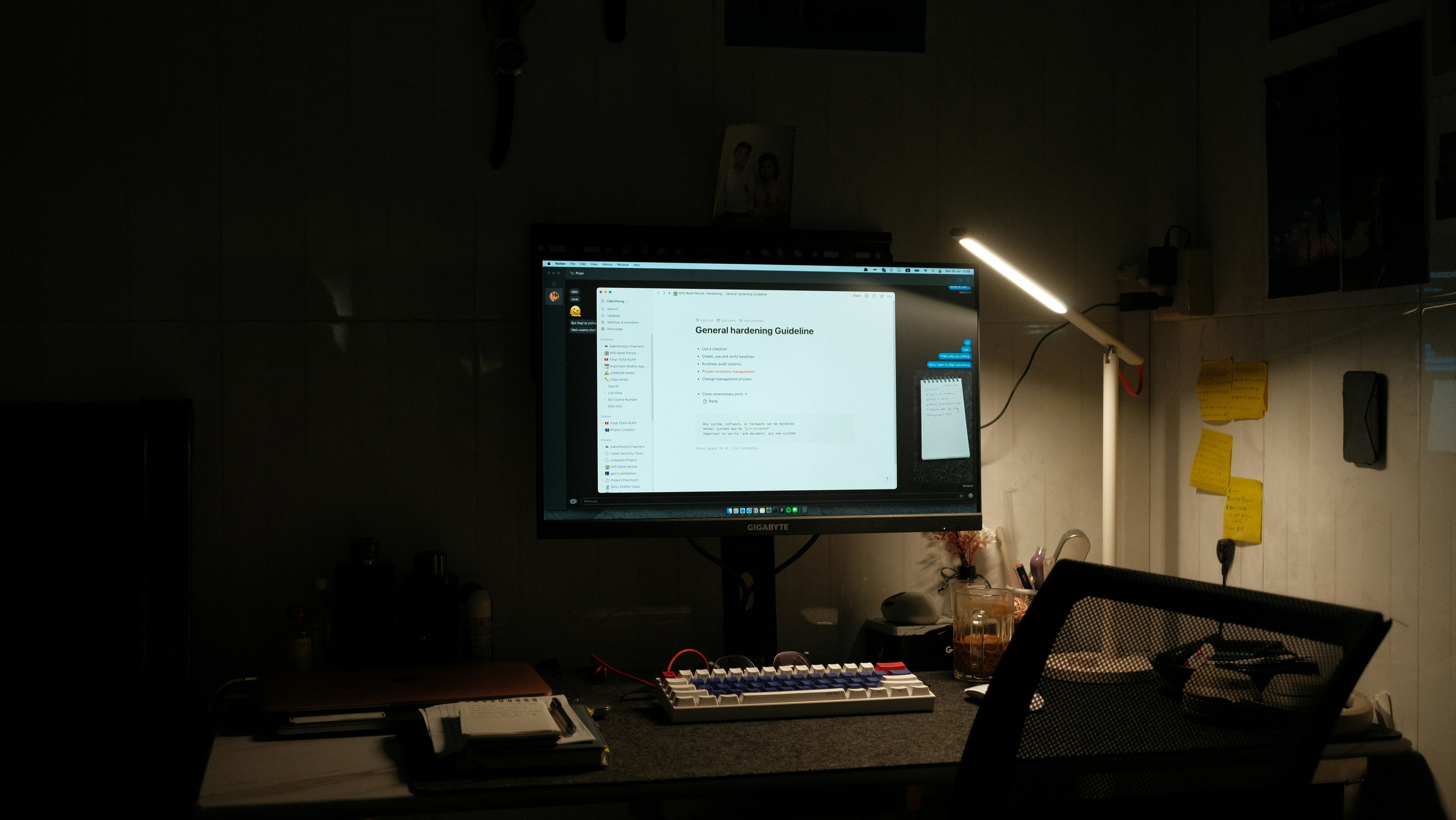
The landscape of cybersecurity has shifted dramatically in recent years. In 2026 a report revealed a startling increase in ransomware attacks. These nefarious incursions into personal and organizational systems are not only proliferating but becoming increasingly sophisticated. In fact, the report highlights a staggering percentage increase in incidents that have left many users questioning the efficacy of their current security solutions. This includes the best antivirus software available in 2026. This poses the question: can you have ransomware attack with a zero day vulnerability?